1.0 Introduction
Sunaum Ltd is a Birmingham based SME retailing in computer components and ready-built computer systems to the general public. Currently goods are sold over the counter directly to customers. This brief report is an endeavour to highlight the factors relating to order processing, fulfilment and shipping; once an order is generated online keeping abreast that these are to conform to consumer expectations.
2.0 Order Processing and Developing Your E-Commerce Web Site
2.1 Customer Relationship Management (CRM)
CRM is the implementation of business strategies that identify and manage customers to derive maximum long-term value from that relationship. The use of CRM requires a customer-centric business philosophy that is often a change from the traditional product oriented of many businesses. This philosophy should be further explored and applied to the business. For example in Ryan Rosenberg’s [1] journal he explains, that queries received by email should be responded to with 24 hours. Therefore a CRM implemented strategy would outline a protocol for effective communication between the business and the consumer.
2.2 Security
When requesting personal data from visitors via the company’s website namely credit card details a SSL[2] connection is the common practice. It is desirable to have a 128Bit encryption.
Browser compatibility and ubiquity[3] are the essential factors. Comodo, Verisign, Thawte, Baltimore and Entrust all provide 99% browser ubiquity.
GeoTrust provide 90% browser ubiquity. Anything less than 99% browser ubiquity will cause the visitor’s browser to show security warnings.
When a purchase is made online, the connection to the server/website needs to be secure. If however the connection is not secure then this will have a dramatic effect on your site. Visitors to the site simply will not purchase at all! Would you give out your personal information, especially your Credit Card details over the Internet on an unsecured connection? Course Not! To show your visitor that you are security conscious and that you have taken steps to provide maximum security, you should host your shopping cart on a secure sever, with a minimum of 128 Bit Encryption. This is known as (SSL) Secure Socket Layer. Your web site on a secure server will produce a small pad lock at the bottom right of your visitor’s browser window; this is a visual confidence boot to your visitor, because it means that the connection to from the visitor’s computer to your web site is secure and no one else can view what your personal information as you type it in. See figure 1.

Figure 1 This is what you see when you first enter a secure site, a security alert. (Windows Vista)

Figure 2 Earlier versions of windows pre Vista like windows XP the security pad-lock will appear at the bottom right.
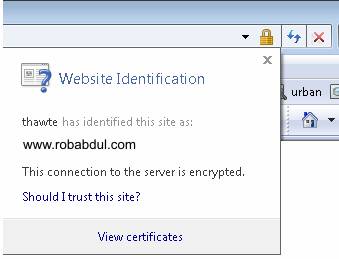
Figure 3 If you double-click the pad-lock the sites security certificate will appear.
Security Certificate
A security certificate is like an electronic claim to authenticity and reassures visitors that you really are an online business and that the authorities validated you with a security certificate.
2.3 Consumer Confidence
With respect to the section above s2.2 Security, I recommend the purchase of a SSL Certificate or the use of a third party vendor (s2.4 Payment Methods) to take payment as they provide greater security. This clearly shows the customer that you have given thought to security and that it’s safe to buy!
2.4 Payment Methods
Various options are available here; these include:
Manually inputting credit card details into the existing ePDQ[4] machine.
Paypal[5] is a third party service, which is a cost-effective way for businesses to accept payments online for a small fee per transaction. This is the most likely method of taking payment online that the author is considering to recommend; mainly because it is has been tried and tested and has proved a real confidence booster to consumers.
2.5 Business Strategies
Online business need to work in partnership[6] with their suppliers to coordinate efforts to improve supply chains. A collaborative relationship with mutual benefits shall benefit the consumer. For example reduced delivery times, overheads, material costs etc.
2.6 Effective Supply Chain Management
In order to incorporate possible MRP[7], ERP[8] systems suppliers must also be up to scratch with, their internal workings of their business and their supply chains. One way to decide on which suppliers are up to standard is to Benchmark them.
You can benchmark your supplier by the following:
- Process Benchmarking: Benchmark performance set by companies doing similar process JIT[9] is the best example.
- Hardware & Software compatibility of ERP systems
- Security
- Reliability
- Flexibility
- Price
- Responding in influx in demand. Research conducted has shown that businesses that have online e-commerce web sites experience greater volumes of sales. Therefore it is paramount that your suppliers can deliver!
3.0 Fulfilment of Orders
3.1 Accessibility
Allowances must be made for visitor’s that have disabilities[10], hyperlinks that are images; a text alternative must be provided. Therefore W3C guidelines must be taken into account for fulfilling orders that are made by users that have a disability.
3.2 Change Management
Research carried out in this section shall help the company understand who in the business would be impacted by e-commerce/trading and identify new business processes. By analysing the potential effects in advance shall facilitate identifying potential future internal communication problems due to changes in business processes.
3.3 Legal Requirements
When checking-out (providing delivery and payment information) on the company’s website, personal data[11] is required from the visitor. This data includes the customer’s name, full address, and credit card details. Registration for the Data Protection Act 1998 is subject to s18 of the Data Protection Act 1998.
Precautions must be taken not to infringe material of other web sites on the Internet[12].
The website should not have any material that is obscene[13]. It is necessary to be aware of regulations governing the Internet.
4.0 Shipping
Fulfilling online orders is still proving to be challenging to e-businesses[14] as going online generally increases your orders and yet customers want goods as soon as possible. Courier services is essential because it is unlikely that deliveries will be made by the company; more so by a third party due to the sheer volumes and geographical locations. CityLink, Royal Mail, DHL, and UPS are just a few examples of courier service providers that need to be looked into to determine which service to use.
5.0 Conclusion and Recommendations
It is recommended that a Back Ordering[15] system should be incorporated in to web sites functionality to retain customers in the unfortunate event that you sell out.
The sheer volume of orders shall have a great impact on businesses ability and proficiency to fulfil and ship orders. It is recommended that the business employ more staff to for order picking and administration.
All the points raised in this report require further research any analysis to derive a coherent and systematic business and web strategies. Due to the recommended word limit the Author has made every effort to show awareness of the issues raised in brief.
6.0 References
Books:
Managing the Data Warehouse
W. H. Inmon, J. D. Welch
Katherine L. Glassey
Published by (1995) John Wiley & Sons, Inc.
ISBN 0-471-16310-4
Business Studies
Ian Chambers (1994)
Published by Causeway press Ltd.
ISBN 1-873-929-09-9
Change Management – A Guide to Effective Implementation
Second Edition
Robert A Paton (2000)
Published by Sage Publications
Management and Organisational Behaviour
Sixth Edition
Laurie J Mullins (2002)
Published by Pearson Education Limited.
ISBN 0-273-651-47-1
Handbook of Logistics & Distribution Management
4th Edition
Jonh L. Gattorna
Published by Gower Publishing Company 1990
ISBN 0-566-07625-X
E-Commerce Doing Business Electronically
Mark Lubbock
Louise Krosch
Published by (2000) The Stationary Office
ISBN 0-11-702392-2
Mastering The Business Environment
Roger Cartwright
Published by (2000) Palgrave
ISBN 0-333-92937-3
Internet:
E-learning strategy online learning strategies
http://www.academyinternet.com/elearning/strategy.html (Downloaded10th March 2003)
World Wide Web Consortium
http://www.w3c.org (Downloaded 10th March 2003)
Journals:
10 Tactics to Promote your Web Site Security
Mark Beamont
InternetWorks June 2002
Don’t Forget the users!
Charls Lowe
E.Business April 2002 Vol 2 Issue 15
Support Your Customers
Ryan Rosenberg
InternetWorks May 2002
Etip Thou shalt not pester
Richard Bradley, Cisco Systems UK
InternetWorks April 2003
[1] Journal, Support Your Customers by Ryan Rosenberg InternetWorks May 2002
[2] Secure Socket Layer – Information Security Standards http://www.diffuse.org/secure.html#S-HTTP
[3] Why is “Browser Compatibility” so important? – Wh?ch SSL http://www.whichssl.com
[4] ePDQ The Barclaycard Merchant Services Internet Payment Engine.
[5] The way to send and receive money online – http://www.paypal.com
[6] Athens E-Journals Article 18 – Measuring Supply Chain Success – Advisor Publications, Inc.
[7] Materials Resource Planning.
[8] Enterprise Resource Planning.
[9] Just In Time Management, a philosophy more relevant to manufacturing of goods.
[10] The World Wide Web Consortium (W3C) Recommendation 5-May-1999 Web Content Accessibility 1.0
[11] The Data Protection Act 1998, Part 1 The Principles
[12] The Copyright Designs and Patents Act 1988 clause 3.3.3
[13] Obscene Publications Act 1959 The publication (whether for gain or not) of material intended to be read, heard or looked at which is such as to tend to deprave and corrupt persons having access to the publication is a criminal offence which carries a maximum sentence of three years imprisonment.
[14] E-Stores Hindered by ‘Logistics Chaos’ http://www.ecommercetimes.com/perl/story/1094.html
[15] www.dabs.com provide a back ordering system for their customers